Each year, new phone models are coming out with bigger and better specifications. But, even if these mobile phones are now packed with software and hardware enhancements, you’ll still need an assorted of mobile accessories to complete the experience. Not convinced? Look on your mobile phone now, you’ve probably had the screen protector or phone cases attached, and most time, your wireless earbuds are all jammed in tightly in your ears. So, if you think mobile accessories are not essential, think twice! When there’s demand, there’ll always be supplies. That said, you’ll find a wide range of mobile accessories, that can range from your essentials like the phone charger, wallet phone case to exotic upgrades like the cell phone tripod, and more. A good question to ask is, “What are the best mobile accessories I should get?”
Assuming you already have some of the basic mobile accessories, however, we’re here to make sure you don’t just settle for the basic. This guide serves the sole purpose to ensure you’ll find the perfect mobile accessories to elevate your mobile streaming or gaming experience. That said, you’ll find interesting mobile accessories that you don’t even know it existed. Read on if you’re interested to know how to take care of your mobile accessories, where to buy mobile accessories, and more. Don’t worry, it’s free!
 What Are The Different Kinds of Mobile Accessories?
What Are The Different Kinds of Mobile Accessories?
Mobile accessories can be interpreted easily as a supporting accessory to enhance your experience whenever you’re using your mobile phone for entertainment or work. The types or genres of mobile accessories are indefinite. But we categorized some of the essentials that you shouldn’t miss out on.
Mobile Phone Screen Protectors
Everybody knows how important it is a screen display to any electronic devices that needs the touch-screen function to operate. That’s especially when a mobile phone nowadays is so dependent on the screen display. Given that we use our mobile phone most of the time for streaming videos, browsing the internet, taking photos; a phone without a screen is almost defying the purpose of a mobile phone in the first place. With that much of the attention given to the screen displays, equal care should be granted too. A good way to start is by identifying the type of screen protectors, the materials, and its purposes.
Though the typical reasons we all screen protectors are to avoid scratches from plaguing our phone’s screen. But, did you know there are also screen protectors that are here to withstand more impactful damages? Find out what’s the best screen protectors you can get today!
Types of Screen Protectors
TPU Plastic Screen Protector
Most of the time, screen protectors come in different forms and features distinctive functionalities that come with the pros and cons. Typically, protectors made from TPU Plastic aims to prevent light scratching on your phones. This kind of screen guard comes in the form of a thin plastic film with or without a color filter. It adhesive and it’s easy to install on your mobile phone. However, TPU plastic screen protectors tend to wear out faster, especially if you’re rugged with your phone.
Tempered Glass Screen Protector
Dropping your phone is a common accident when it comes to mobile phones. Sudden movements can lead to your phone slipping-off of your hand or pockets accidentally. If you are looking for a TPU alternative, the tempered glass screen protector is the one for you. This kind of screen guard is the most durable out of the three. It can withstand scratches and fall damage. But if you drop your phone from an extensive height, the tempered glass will surely shatter. This is normal as it gives your phone that extra layer to protect the screen from damage.
PET Plastic Screen Protector
So, if your phone tends to slip off your hand frequently, the TPU material might not be the best choice. Instead, you should opt for the PET Plastic screen protector as its material is far more scratch-resistant. It won’t cost much considering its durability. But the downside is, it is harder to remove as compared to TPU screen protectors. Another downside of TPU plastic is that it is not that resistant to fall damage.
Purpose of Using Screen Protectors
iCarez [HD Anti Glare Matte Screen Protector for Apple’s iPhone]
MANTO Full-Coverage Tempered Glass Screen Protector for iPhone
Supershieldz Anti-Spy Tempered Glass Screen Protector for iPhone
Multi-Layered Screen Protector
This type of screen protector is the best if you’re seeking for extensive protection from knocks and scratches. As the name implies, this kind of screen guard has many layers for added protection. It’s thick enough to withstand a stronger impact. The substantial layers are here to make sure your phone display is well-intact even if the screen protectors are shattered.
Ultra-Clear
Ultra-Clear variants protect your screen while also giving maximum clarity. If you crave a screen protector that protects without unnecessary tints, glares nor extra effects, this is a great fit. It serves the purpose and you’ll be able to see and feel your screen as if there’s nothing is on top of it.
Anti-Glare Screen Protector
The anti-glare screen protector can help to reduce glares on your LCD screen. This type of protector can aid in reducing eye strain which is ideal for users who’s using devices under bright light exposure.
Typically, it features a matte finish coating that’s perfect to reduce fingerprints left on the screen. It usually comes with anti-scratch coating and the non-adhesive backing leaves zero to non-sticky residues on the screen. The only downside for this type of screen protector is it tends to decrease the clarity.
Privacy Protect Screen Protector
Privacy protectors are made to shield your screen content from the prying eyes. It’s created in a way to make your screen content less noticeable when the phone is tilted at an angle. If you’re a business user who reads company data or personal emails on the go, you might want to opt for this.
Mirror Screen Protector
Mirror Screen guards allow an effect that is the same with chromed-out products. What it does is it allows your phone screen to produce a clear reflection as a mirror would. This is perfect for people who use their phone screens to act as a secondary mirror and is especially helpful when applying make-up or checking for facial irregularities.
How to Apply Screen Protectors Properly?
There’s only one reason why it’s hard to apply screen protectors — wrong techniques. Though many would have just preferred to seek professional help, you wouldn’t have guessed that it’s surprisingly easy to just do it at home. Not only it’s cheaper to DIY, but it’s also far more convenient. All you need is the correct tools and skills to do it. However, we don’t deny you might need some practice, but once you’ve got a hang of it, you’ll probably never want to look for any specialists anymore.
One of the most crucial steps is by choosing the correct type of screen protector. Regardless if it’s anti-scratch or anti-spy protectors, all you need is to decide on a screen protector. The last thing you want is to peel and sticks your screen protectors over and over again. Once you’ve decided on a screen protector, here’s what you need to stick them flawlessly.
1. Clean your screen with alcohol wipes. Make sure there’s no fingerprints or dust on the screen before you attach the screen protector.
2. Once you’re done, peel off only a quarter to half of the protective film off the screen protector to reveal the adhesive. Align the screen protector to your screen’s display, adjust accordingly before you stick it onto the screen.
3. Do not install the whole protector directly onto the screen. Instead, slowly make your way to adhere the screen protector from top to bottom to avoid air bubbles. We recommend you to use a towel to rub the layer as you’re applying it.
4. Once you’ve placed the screen protector, you can remove the trapped air bubbles by pushing out them out of the screen. Do note that you might want to apply some force to get them out of the way.
Cables for Mobile phones
Small electric Multi-adaptable Charger Cables [Micro-USB, USB, Type-C]
Anker Powerline+ Micro USB [Extra-Long, Durable, Premium Cables]
Mobile Phone Cables for Android Devices
Type-C is now common especially when it comes to newer devices. This type of cable allows data to transfer faster from your device to its destination. USB-C cables also allow chargers to increase the power that they transfer to your devices. Type-C cables are also starting to replace audio jacks in some devices.
Micro-USB is the most popular form of cables used on mobile devices. You can use this for charging phones, transferring data, and more. But, Micro-USB cables are being replaced by Type-C because of the better functionality
Mobile Phone Cables for iOS Devices
USB-C technology is also used by Apple for its mobile devices. You can see it used on Lightning-USB-C hybrids as well as in Card Reader adaptors. With Apple’s popularity, third-party companies have also started selling their cables.
Lightning cables are an Apple signature when it comes to mobile devices. You can use this cable to charge iOS devices and connect them to a Mac computer. Lightning cables usually come with a Micro USB or Type C end. It can also come connected to an adapter or other accessories such as cameras.
Last but not least is 30-Pin to USB Cables. These have been a long staple to Apple products. Its purpose is for it to see use in the majority of Apple products.
HDMI Cables
HDMI cables are what people use to connect smartphones with TVs and monitors. These kinds of cables are also used on gaming consoles and computers. HDMI allows the transfer of high-definition media from the input and the output. Some cables can be directly connected to phones while others need an adapter.
To connect a phone to a monitor or tv, you should know what HDMI cable to get. If you prefer a direct connection, find an HDMI cable that is compatible with your phone’s input. Lightning, USB-C, Micro-USB, and even 30-pin ports need the proper cables. If you can find a cable that is the same as your phone, then it’s smooth sailing from there. Just connect the cable to your phone’s port and connect the HDMI end to your TV.
But, if you can’t find an HDMI cable for your phone, the next alternative is via an adapter. All you have to do is connect the adapter to your smartphone. Next, connect the HDMI cable to both the adapter and TV. Once that’s complete, your phone is now connected to a TV or monitor.
Another thing to take note of is doing research ahead of time. Your phone may not be capable of supporting HDMI features.
Tips to take care of your cables
Cables are one of the most replaced accessories when it comes to cell phones. Often, this is a result of multiple uses or the user’s negligence. One good way of protecting your cables is by storing them properly. Do not roll the cable around the charger or device when storing them. Instead, roll the cable around your palm and use a velcro strap to secure it.
Another way a cable gets damaged is near its ends. This is a result of excessive usage and carelessly pulling on the cable. It can also be a result of animal bites especially pests that live in your home. One way of countering this is by wrapping a metal or plastic coil on the ends of your cables. This will prevent animals from gnawing on your cables. This will also prevent objects from scratching your cables’ ends.
Smartphone Projectors
Smartphone projectors are a way to elevate your next presentation or movie night. Connect your smartphone to a projector and enjoy visuals than what your phone will allow. Aside from watching movies or conducting office presentations, a projector offers more functionalities than you can imagine. The limits are only bound by what you can imagine doing with it. Learn what’s the best smartphone projectors that worth its price tag. In case you’re unsure what’s the best way to fully utilize it, we’ll show you how to use a cell phone projector precisely. Pick up the skill as we show you how to connect, to take care, and to make the best out of your investment in a projector.
Mobile Phone Holders & stands
We know it’s inconvenient to hold onto your mobile phone the entire time when you’re streaming a movie or a video. That’s when a mobile phone stand comes in handy to save the day. Though its functionality might not be the most versatile, it’s helpful in many ways. Regardless if you need a cell phone holder to — keep your mobile phone in place, to secure its position for better navigation while you’re driving, or for other purposes; it’s reliable enough to do the job for you.
Phone holders can come in different sizes, colors, models, and distinct materials. You’ll find compact phone holders that are easy to transport with, but, also with those that are bulkier to withstand the weight of your mobile for better stability. While there are plenty of options in the market, we narrowed down some of the best phone holders that are useful in the car or on your desk for you.
cell phone chargers
Chargers for phones and other mobile devices are now becoming a necessity. That’s especially when the world is now heading towards an age dominated by electronic gadgets. As good as they were, everything does have its lifespan. That said, even your mobile phone with a large battery capacity will be depleted. That’s when these chargers come in to save the day. With various demands nowadays, chargers available in the market come in different shapes, sizes, and compatibility. Some of these only work with a specific OS or USB type, while some are made to be adaptable that caters to a wider demand.
Believe it or not, chargers feature more functionality than just it’s the primary uses. The most common one is the plug-in charger that you insert in a socket for it to work. However, some chargers can power-up your phones without inserting a jack or USB. The result? You’ll find wireless chargers available for your convenience and solar-powered phone chargers for people who want to lessen their energy footprints. Then, you also have portable chargers and power banks. These devices will allow you to charge your phone whenever and wherever. In case of an emergency, these devices are your best friends.
There are numerous types of chargers for different phones, getting one should be based on your preferences.
smartwatches
Before, watches were only used to measure time. Seeing what time it is or recording a lap was one of the few functions of a watch. But now, watches come with an assorted of functions including — the call function, navigation function, fitness tracking, and more. Though it still features the basic function to tell the time, these smartwatches are smarter in a sense to help you do things without the actual electronic gadgets. A fit for the current spectrum, smartwatches function more or less like smartphones. They can show notifications and allow you to answer calls anytime anywhere even underwater. How it works is pretty straightforward. All it takes for it to work is by connecting your smartwatch with the Bluetooth function.
An additional function to your basic watches, smartwatches usually come with the function that’ll allow you to stream music on-the-go. Aside from that, you’ll find a health tracker to monitor your vitals. The health analysis is especially helpful to help you understand how your body works and gives you a head up in case of any irregularities.
But, not all smartwatches are made equal. Some run with a specific OS and can only connect to a specific model or brand of a mobile phone. An example of this is kids’ smartwatches that are made to track their whereabouts and safety or fitness trackers made for people who love the outdoors. Then, you have waterproof smartwatches that have similar features but are more for active people.
Fitness Trackers
Speaking of fitness trackers, these are devices allow you to sync the data to your mobile phone. Regardless it’s to tell the time or to analyze your daily activities. If smartwatches aim to be an extension of your device, fitness trackers is the best accessories to complement your mobile for your health. These trackers or bands are best to track your daily activities and to give you an overview of your health. The upshot? Not only it’s stylish, but it also works well to check your heart rate, calories burned even when you’re at an absolute steady motion. A fitness band can also measure your speed and how efficient you move. Then, you can take note of all the measurements to see your improvements.
So how do you connect a fitness tracker to your phone? Well, you can connect it via Bluetooth which will pair up with a corresponding app. Yes, you will most likely need to download an app if you want to sync your tracker–unless specified.
cell phone Cases
Cell phone cases are not just for aesthetic purposes. They are also capable to function differently according to its feature. While most phone cases is made for the aesthetic purpose, others are built to have more resistance and can protect your phone from taking the knocks. Also, those mobile cases that can work as wallets, an extra battery pack, or make with a specific design to your everyday outdoor use. If you’re interested to find out what are the best phone case brands to make your pennyworth, here it is.

Heavy-Duty Cases
Beautiful things are often fragile in most cases. While your aluminum finished iPhone certainly looks stunning. But, if you’re those who love adventure, knocks are unavoidable.
Prevention is better than cure. Hence, here’s the best heavy-duty material you should consider the maximum protection for your mobile phone.
Types of Heavy-Duty phone cases:
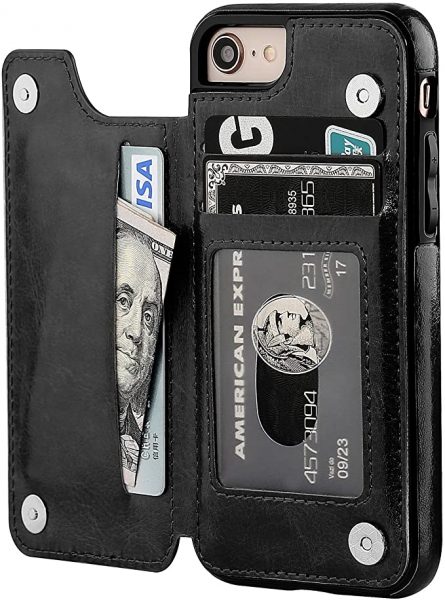
Phone Wallet Cases
Travel light is possible with a phone case that does double duty as your wallet. It won’t cost you more but convenience is at your fingertips.
Phone wallet cases are a great investment. Not only they hold essentials, like a credit card, cash, metro card, and work ID, it also protects your phone from the damages. Find the best folio phone case here.
Types of Phone Wallet cases:

Smart Phone Cases
As the demand for convenience continues to spike, manufacturers are actively seeking for a way to bridge the gap. Hence, smartphone cases open up a new dimension to satisfy demand.
You’ll find a battery charging phone case, LED cases, and more. Find the best waterproof phone case you’ll ever need.
Smart Phone cases type:
how to choose a phone case?
When buying a case for your mobile phone, you should take into consideration a few things. First, you should know the sizes of your mobile phone and make sure the chosen ones are compatible with your phone.
Another thing to consider is the material of the phone case. You pay for what you get, so don’t expect a cheap phone case to last an eternity. That said, if you’re those who are keen on searching for the perfect phone case for maximum protection and durable, opt for a rugged phone case or carbon fiber phone case. Though you might expect to pay a more premium price for its quality. However, if you prefer something that is more aesthetically pleasing, a rubber, silicone or plastic phone case might be something for you. A worthy note is that plastic phone covers aren’t that durable while silicone material phone case it’s more prone to dirt. As for convenience, a phone wallet is perfect for those who are always on the go. If you’re into sports, opt for an armband phone case, it’s convenient and sturdy enough to accommodate your needs.
A good way to protect your phone cases is to stay away from chemicals products. That said, detergent, perfumes and such are a big no. As for plastic phone case, try to keep them away from sunlight, it’ll deform the shape and leaving sticky residues on your mobile phone. Learn the correct way to DIY your phone case for the perfect phone case you ever wished for.
Here are some of the reliable phone case brands we can recommend.

Luxy Lemon
Luxy lemon features a wide range of mobile accessories that range from phone cases, wireless charging, lens protection, screen protectors, and more. One of the more popular products on Luxy Lemon is their battery phone case and it received overwhelmingly good reviews. So, try it and let us know what you think.

Casetify
Expect to find a huge range of phone cases, accessories on Casetify. Welcome home with your custom design phone cases, sling case, latest, and trendiest phone cases on Casetify. It’s affordable and the quality won’t disappoint.

Speck
Speck prioritizes on quality. Though it might not have the trendiest and most aesthetically pleasing phone cases, Speck phone cases are sturdy and durable.

Razer
Most Razer phone case comes with microfiber lining that can sustain the knocks. Made with high-quality silicone, PET plastic and more, Razer’s phone case features sleek, elegant yet presenting the gaming aesthetic every gamer craves for.
cell phone camera lenses
Cell phone cameras are getting more powerful with every new release. The gap between traditional and mobile photography is starting to lessen. But, that doesn’t mean that these cameras can satisfy everyone. While on the bright side is there are plenty of mobile accessories like the camera lens kit to turn your passion for photography into a real thing without overspending on professional camera equipment.
Depending on the effect that you want, there are a variety of lenses from — fisheye lenses, wide lenses, color filtered lenses, and more. Though a camera lens is supposed to accentuate your photographs, not every one of them does what it’s supposed to do. Find out what’s the best camera lens you should be getting. We make sure these lenses are worth its price tag and it’s an investment that you won’t regret. Don’t worry, we explained the difference in all of these lenses just so you can pick and choose the perfect one to make your money worth.
selfie sticks & cell phone tripods
As important as having a great time while you’re traveling or having a gathering, it’s almost essential to take a photo or two to capture these memorable moments. Not only it’s useful to help you refresh your memory, but it’s also fun and informative to share these moments with your friends and family. Though sometime you might not be traveling with a companion, a selfie and a tripod is all you need to take these photos with minimal help. All you need is to set up these gadgets and you’re off to go. So, whether you fancy a selfie or to take some quirky photos of your travel adventures, they are here to save the day.
Nowadays, selfie sticks and tripods come in all sorts of sizes, shapes, and functions. Though most of them work more or less the same, still, there are some criteria you need to consider. That’s especially the material used, the functionalities, it’s convenience, and more. We rounded up some of the best tripods and best selfie sticks you’ll ever need for your phone. Whether you’re taking a photo, videos, or anything of the sort, we got you covered. Say bye to those shaky and blurry photos with these tripods.
Best Bluetooth speakers
Whether you’re looking to study, throw a party, or chill, speakers are a good tool to enhance the mood. These devices allow you to play your favorite songs and though some speakers require a jack to your phone while some don’t. But with the advancement of technology, most speakers can be synced via Bluetooth. All you need is a stable connection and you’re free to play any music any time anywhere. The good thing about this is that you don’t need to spend on wires and cables. Plus, some Bluetooth speakers are also portable and you can use them whenever you want. The only downside on Bluetooth speakers is that you have to be aware that your device needs to be in a certain to function properly.
When you’re considering a Bluetooth speaker, it’s best to know its purpose. Is it outdoor or something else? Preferably, a waterproof speaker is more durable to withstand the harsh weather condition, while smart speakers like the Echo dot or Apple Home should be for indoor use. A portable compact Bluetooth speaker is best for outdoor camping or for traveling. It’s much more convenient and the music quality is not too dubious.
Best headphones, headsets & Earbuds
| Types of Headphones | Top 3 Must-Buy Headphones | Price Range | Next Step |
|---|---|---|---|
|
$199.00 – $399.00
|
|||
|
$9.99 – $90.00
|
|||
|
$14.95 – $229.90
|
|||
|
$198.90 – $229.90
|
|||
If you’re looking to listen to your favorite tracks with a little discretion, this section is for you. Whether you are working out, studying or just an audiophile, there is a listening gadget for you. Before we venture further, we have to discuss what is the difference between headphones, headsets, earphone, and earbuds
The difference between a headphone and headset is that the latter features a microphone built-in to it. This allows you to take calls or use them when playing games with your friends. The difference between earbuds and earphones is that the former goes into the ear canal while the other stays out of it. If you’re looking to see how wireless headphones work or wondering what are some of the best budget headphones you can get, we got you covered.
Headsets, on the other hand, will allow you to take phone calls. While some gaming headsets are great to put in the mood for a challenge.
Bluetooth keyboards
Have you ever had trouble typing using your touchscreen? Do you want to type faster with veracity? Well, we’ve got a solution for you, Bluetooth keyboards! This kind of keyboard will allow you to type as if you’re using a laptop or computer. This is also good for people who are having trouble seeing the keys in on small screens like mobile phones or tablets. All it takes for this mobile accessory to work is by connecting and pair your device with your mobile phone with the correct connection. This is especially useful when you’re working on the go while you’re commuting. In case you left your laptop back at home, you can access your business document on mobile and these keyboards are here to help you navigate your work more efficiently. Find the best Bluetooth keyboards here.
 Best Mobile Gaming Accessories
Best Mobile Gaming Accessories
Mobile gaming has seen an increase during the past decade. Not only can we play RPGs and single-player games but now we can play more. MOBAs and shooters are dominating the mobile scene. Even industry giants are stepping in to take advantage of the increase in interest. You can even see mobile games being the center of Esports events across the globe.
If you’re thinking of stepping up your games, you might want to consider purchasing a few mobile gaming accessories to your arsenal. These include controllers, VR headsets, and gaming headsets.
Gaming controllers
Controllers will allow you to navigate games like traditional consoles. You can map out controls and have more emphasis on the action you want to perform. Not only that, but controllers will give you tighter inputs.
There are many controllers that you can use for your mobile phones. Some of these are even created for the OS of your choice. They can also be connected via wired connections or by Bluetooth. Here are guides for the best gaming controllers for Android users.
vR headsets
Another great advancement in mobile gaming is the addition of virtual reality compatibility. This allows you to play VR games or watch movies on your phones. Of course, the most important thing is for you to have a VR headset and your phone should be able to support VR features. Then, you can connect them via an app that your headset will need or install them into the headset. Once all that is done, you can now enjoy VR anytime and anywhere.
 How To Buy Mobile Accessories?
How To Buy Mobile Accessories?
A good question to ask when you’re doing your research on which mobile accessories are best is “What do I need?” Let’s say if you’re those who often drop your phone, a phone case might be a good idea. If not, are you those who are into mobile phone photography? If yes, a camera lens might be something for you. Ultimately, ask yourself which part of your mobile phone you want to upgrade and how urgent it needs to be upgraded.
Determine the quality of the product
First, find out the quality of materials used in the product. If what you’re looking for is longevity and durability, then, you have to take a look at the materials used in making the product. Better materials produce a sturdier product that can stand bumps and bruises. But, expect that these items will go for a more premium price as compared to the basic ones.
Do your research
Another way of researching ahead is by reading reviews on e-commerce sites and YouTube. The more reviews an item has, the bigger the sample size. Remember, a product with a high rating from many reviewers is better as it is more reliable. YouTube reviews can give you a better visual review along with the reviewer’s opinions.
Look for mobile accessories guides
Look out for mobile accessories buying guides if you want to see the best choices for a particular product. You also can check the feedback from previous customers to get to know how the product performed. This is also a good way to have an idea of the seller’s customer service.
 Where Can You Buy Mobile Accessories?
Where Can You Buy Mobile Accessories?
When buying mobile accessories, the best way to go is by buying through online shops. You can visit an e-commerce site right now like Amazon and see their catalog. Amazon and other online stores allow readers to search the product and compare it to others. This a great feature that allows a consumer to see the pros and cons of buying a certain item. Online shops also have the specifications for each product.
E-commerce sites also allow you to shop without leaving your room. Just browse their catalog via the internet and just add everything you want in your cart. Check out and all you need to do is wait for your package to arrive. It’s simple, safe and you don’t have to travel elsewhere.
 How to Sell Mobile Accessories?
How to Sell Mobile Accessories?

If you think about it, selling mobile accessories is a good idea. People will try to look for accessories that can help in their hobbies or protect their phones. There is also an endless supply of new accessories getting released. This is to cater to the latest smartphones that are being released to the public. The question now is, how to sell mobile accessories?
Well, the best way is to do market research to gauge what people in your area are interested in. This is applicable if you are planning to market locally. You can take the results and start focusing on those products. Another way to sell mobile accessories is by using e-commerce sites and social media. Besides, you can also sell mobile accessories on sites like Amazon and eBay. Then you can make use of services such as Paypal to make the transaction faster and safer. But, if you’re planning for a more interactive approach, you can make use of social media sites. Facebook has a Marketplace which will allow you to sell your items.
You can also do it on Facebook groups that allow the selling of mobile accessories. Selling on Facebook will allow your customers to send you a message and you can respond in real-time. You can also create a page for your business if you don’t want your profile to get bombarded. But, if you have a budget you can always build a simple website for your products. You can then promote your website on social media.
Is the mobile accessories business worth doing?
The answer can be ‘Yes’ or ‘No.’ Depending on how you see it, and what do you expect as a return. Generally, it’s easy to create a business out of selling accessories for phones and other mobile devices. You can either sell accessories you’ve made yourself or buy in bulk.
Creating your accessories will allow you to control everything from the cost, raw materials, and labor. This type of strategy can start as a DIY project that you can do at home. For example, you can create or design cases for smartphones. Then, release these cases via batches so that it does not overwhelm you. Take more orders if you see an increase in demand and if you got more hands to help you. This will allow you to produce items faster and increase orders. Then, you can market an upcoming design you’ll release as part of your next line of products.
There are plenty of ways to profit by selling mobile accessories. One of the ways is by increasing the designs or products for your upcoming releases as labor and capital go up. This will allow you to offer more products to patrons and attract new customers. Another way of selling mobile accessories is buying through wholesalers. You don’t have to worry about the cost of raw materials and labor. All you have to do is buy phone accessories by bulk and you can then sell them for retail.
An advantage of this option is that you can sell them right away. All you need to do is to reorder an item from a wholesaler if your stock is getting low. Otherwise, you can opt to be an authorized retailer of different brands which will give your business a bigger profile. So, is it worth it or not is down to how you interpret it? Some argue the mobile accessories business is great but some think otherwise.
 How to Repair Mobile Accessories?
How to Repair Mobile Accessories?
Repairing or troubleshooting a mobile accessory is highly dependent on the product at hand. Of course, you cannot use a specific method for different products. If you are interested, our articles have stepped on how to prolong the lives of your mobile accessories.
There are also videos online showing how you can repair certain accessories.
Related Articles
- How to Clean Phone Cases Effectively?
- Where to Buy Cell Phone Cases?
- How Does A Gameboy Phone Case work?
- Best Fitbit Replacement Bands